A security vulnerability is a system weakness that can compromise confidentiality, integrity or availability. When a vulnerability receives a high score in the Common Vulnerability Scoring System (CVSS), it’s natural to want to reorganize your priorities. A CVSS score is a highly focused input, however, and does not provide a full story. Additional factors such as exploitability, exposure, timing and the safest fix path are vital to decision making.
Today’s enterprises must actively protect against threat actors or adverse events that can harm their environments. In addition to identifying security vulnerabilities, teams must know what to fix first and how to fix it safely. Through a disciplined process of inventory, prioritization, mitigating and then verifying, you can successfully reduce vulnerabilities and improve long-run stability.
What are security vulnerabilities?
Contents
- 1 What are security vulnerabilities?
- 2 Common types of security vulnerability
- 3 Real-world examples of security vulnerabilities in action
- 4 Security vulnerabilities management: prioritizing and assessing risks effectively
- 5 Preventing security vulnerabilities with SUSE’s open source approach
- 6 FAQs about security vulnerability
A security vulnerability is a flaw, misconfiguration or other weakness in your software, hardware or IT processes. More specifically, it is a flaw that could be exploited to cause harm.
Notably, a security vulnerability is not itself an attack. Rather, it is a condition that leaves the door open to attacks. Security vulnerabilities also differ from threats, which refer to the entities that have potential to harm your system. In addition, they are different from exploits, which refer to the methods that attackers use.
What are vulnerabilities?
Not all vulnerabilities are security-related. In technology, the term can refer broadly to any weakness in a system’s design or operation. A software bug, for example, may degrade performance without exposing systems to threat actors.
Some vulnerabilities are caused by outdated software components, misconfigured access controls or unsafe default settings. Others stem from complex integrations or overlooked dependencies. Rushed deployments or long-standing technical debt can both contribute to these issues.
The business impact of security vulnerabilities
Regardless of exploitation, vulnerabilities create disruptions and related ripple effects. They lead to unplanned patches, emergency change windows, increased alert volume and unexpected documentation efforts — often at the expense of planned projects. Breaches can be costly to investigate and remediate, and regulatory fines or contractual penalties can further raise their financial impact. In addition, unresolved vulnerabilities can negatively affect compliance standing, customer trust and organizational reputation.
Common types of security vulnerability
Security vulnerabilities appear in many forms. Some are widely recognized risks, while others are newly emerging.
Across estates, examples include:
- Software flaws and dependencies, including memory safety issues, logic errors and outdated libraries. A small defect can become high risk when it is reachable, exposed to the internet or combined with broad permissions.
- Misconfiguration and identity gaps, such as overly permissive roles, open ports, default credentials or excessively broad network rules. Attack paths can expand suddenly in these contexts.
- Secrets handling, including credentials or tokens that are accidentally stored in code, images or logs. Once discovered, these shortcuts allow attackers to bypass authentication, fueling lateral movement.
- Supply chain issues, such as unpinned dependencies, unsigned artifacts and compromised registries or mirrors. Tampered components can spread quickly across environments and are hard to spot without provenance checks.
- Misconfigured cloud and Kubernetes security configurations, such as mismanaged access controls, exposed dashboards or insecure defaults in clusters. Shared services and public endpoints can widen the potential blast radius.
- Weak segmentation, including flat networks and shared control planes that let attackers move laterally. Without strong isolation, a single foothold can lead to major disruptions.
Real-world examples of security vulnerabilities in action
When vulnerabilities surface in critical systems, timing and context determine how serious they really are — and how urgent a fix should be. For example, a widely known flaw with active exploitation reports becomes even more dangerous when it appears in an internet-facing service.
The specific business cycles of your organization can also influence response. A medium-severity database flaw may be too risky to patch immediately before a reporting deadline. By applying compensating controls and fully documenting the deferral, you can stabilize operations and close the resulting audit item in the next review cycle.
Similarly, there are situations where the fastest path may not be the safest option. Upon discovering a container image with an outdated library, you might choose to mitigate the risk with an immediate configuration change. During the next sprint, you can rebuild the image using a patched base image. This approach lowers short-term exploitation dangers without disrupting delivery schedules. It can also minimize the possibility of introducing instability because of rushed changes.
Security vulnerabilities management: prioritizing and assessing risks effectively
A CVSS score is just one signal. Effective, real-world prioritization requires evaluating multiple sources of information — including exploitability, exposure or blast radius, business timing and the safest fix path.
The following steps can help translate this approach into practice:
Build a reliable inventory
A good prioritization decision depends on good information about your environment. Maintain an up-to-date inventory of servers, containers, virtual machines, clusters and other assets, including the software they run. Assign clear ownership for each item and track their versions, configurations and dependencies. When possible, fold inventory checks into your normal change flow.
Don’t overlook niche systems
Discovery isn’t complete if it ignores the long tail. Edge devices, specialized appliances and legacy application servers often run different Linux variants or vendor-hardened builds. Without an explicit approach for these platforms — including coverage in scanning, patch channels, owners and maintenance windows — they can remain unpatched and unmonitored. Include them in the inventory, label their constraints and define a minimal remediation path so that they don’t become silent amplifiers of risk.
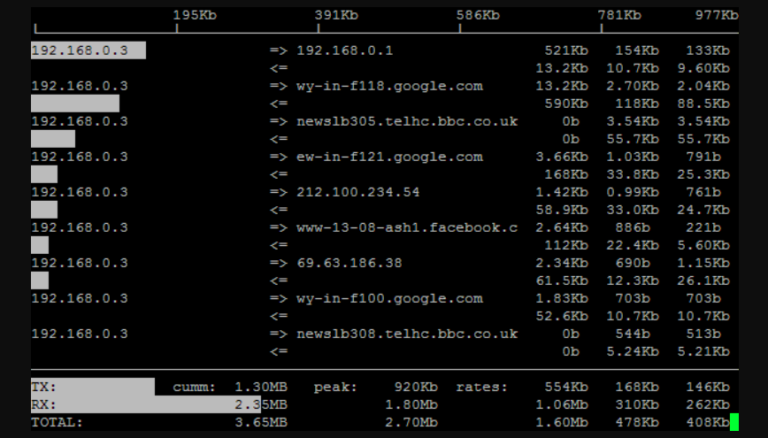
Prioritize by exploitability and active threat
If there’s no known way to exploit a flaw, a high score carries less risk. Conversely, a moderate score can take top priority if there is evidence of attackers currently and actively exploiting the weakness. Use trusted threat intelligence and known exploited vulnerability lists to determine which issues are most urgent. Pair that information with what you see in your own telemetry — such as blocked attempts, anomalous traffic or repeated probes.
Correlate scanner findings with vendor advisories
A common friction point appears when scanners or CVE feeds look only at upstream version numbers. For example, a package in Enterprise Linux may be flagged as “vulnerable” because its version string looks older — even though the security fix has been backported to that supported version. Recent upticks in kernel CVE reporting can amplify this noise and flood queues with false positives.
Be sure to treat version-only flags as hypotheses to validate. Check the vendor’s security advisories or machine-readable feeds — such as OVAL/CSAF — to confirm patch status. Tune scanner plugins to recognize vendor backports and CPEs where possible. Record decisions with advisory IDs or other evidence so that exceptions are time-boxed and auditable. With these practices, teams can stay focused on real exposure, and you can minimize unnecessary tension between security and operations.
Weigh exposure and blast radius
Consider where the vulnerable asset lives, including how accessible it is to attackers. Internet-facing systems, shared service accounts or poorly segmented networks are more likely to magnify blast radius. A flaw with broad identity scope should outrank the same flaw buried behind layers of segmentation.
Balance severity, impact and timing
Critical systems often require carefully scheduled updates to avoid disruption. In real-world settings, you must consider maintenance windows, regulatory deadlines and the role of the asset in business processes. When working to reduce security risks, it is still important to avoid creating new problems. In the event of a deferral, apply compensating controls and set a review date to minimize the possibility of drift.
Identify the safest strategy
Not every vulnerability demands an immediate patch. Configuration changes or compensating controls can provide short-term protection when immediate patching isn’t yet ready or possible. For example, in the context of container security, switching to hardened base images or signed containers can reduce risk in tandem with runtime mitigation.
Treat patching as part of vulnerability management
While patching is essential, it is not the whole program. Patch management distributes and applies updates. By contrast, vulnerability management decides what to address first and how to reduce risk safely. In most cases, a patch-everything-first approach is both inefficient and risky. Issues like misconfigurations and unsafe defaults are not patchable by their very nature. Other issues may demand speed because they are internet-exposed or currently being exploited. Avoid treating every CVE as an urgent fix. Instead, order the work by real-world danger and window for safe change.
Verify, measure and iterate
After remediation, rescan or retest to confirm the issue is resolved. To grow your team’s shared knowledge base, track metrics like mean time to remediate, backlog trend and exposure of known exploited vulnerabilities. Review exceptions regularly, and adjust processes based on what works best.
Preventing security vulnerabilities with SUSE’s open source approach
Without a comprehensive approach to security vulnerability management, vulnerabilities can go unnoticed until you introduce a new scanner, an auditor digs deeper or a breach hits the news. Organizations are most successful at preventing vulnerabilities when security is built into daily operations. Standardizing and embedding preventive measures can reduce noise, lower risk and keep remediation costs in check. Small, repeatable actions — like staging changes, prioritizing by context and verifying outcomes — will strengthen security posture and help create long-term operational resilience.
As environments evolve, best practices should travel with you. Open standards and transparent methods help teams stay in control, streamline audit preparation and shorten exposure windows. SUSE supports these goals through portable, interoperable approaches that work across estates. For teams managing mixed Linux distributions and modern Kubernetes deployments, SUSE can help reduce risk without creating lock-in. For example, a tool like SUSE Multi-Linux Manager centralizes and automates patching and compliance for a wide range of Linux distributions. As a result, you can manage your entire inventory from a single console, confident that vulnerabilities are fixed consistently and efficiently.
Explore SUSE’s security solutions — and unpack the power of open security foundations.
FAQs about security vulnerability
How can vulnerability scanning tools help protect my organization?
Vulnerability scanning tools help protect organizations by identifying issues early and at scale. These tools will help you uncover misconfigurations, unpatched components and deviations from baseline.
What is the difference between a security vulnerability and an exploit?
A security vulnerability is a weakness that attackers can use to compromise a system. An exploit is the specific method or code that the attackers use when taking advantage of a weakness. For example, an unpatched bug in a web server is a vulnerability. The malware used to gain system access, because of the bug, is an exploit.
How often should a security vulnerability assessment be conducted?
You should conduct security vulnerability assessments regularly. Most organizations tie frequency to the typical rate of change in their IT environments and their unique risk profiles. In addition, cadence might temporarily increase when you add new assets, make major releases or adjust your architecture.
(Visited 1 times, 1 visits today)